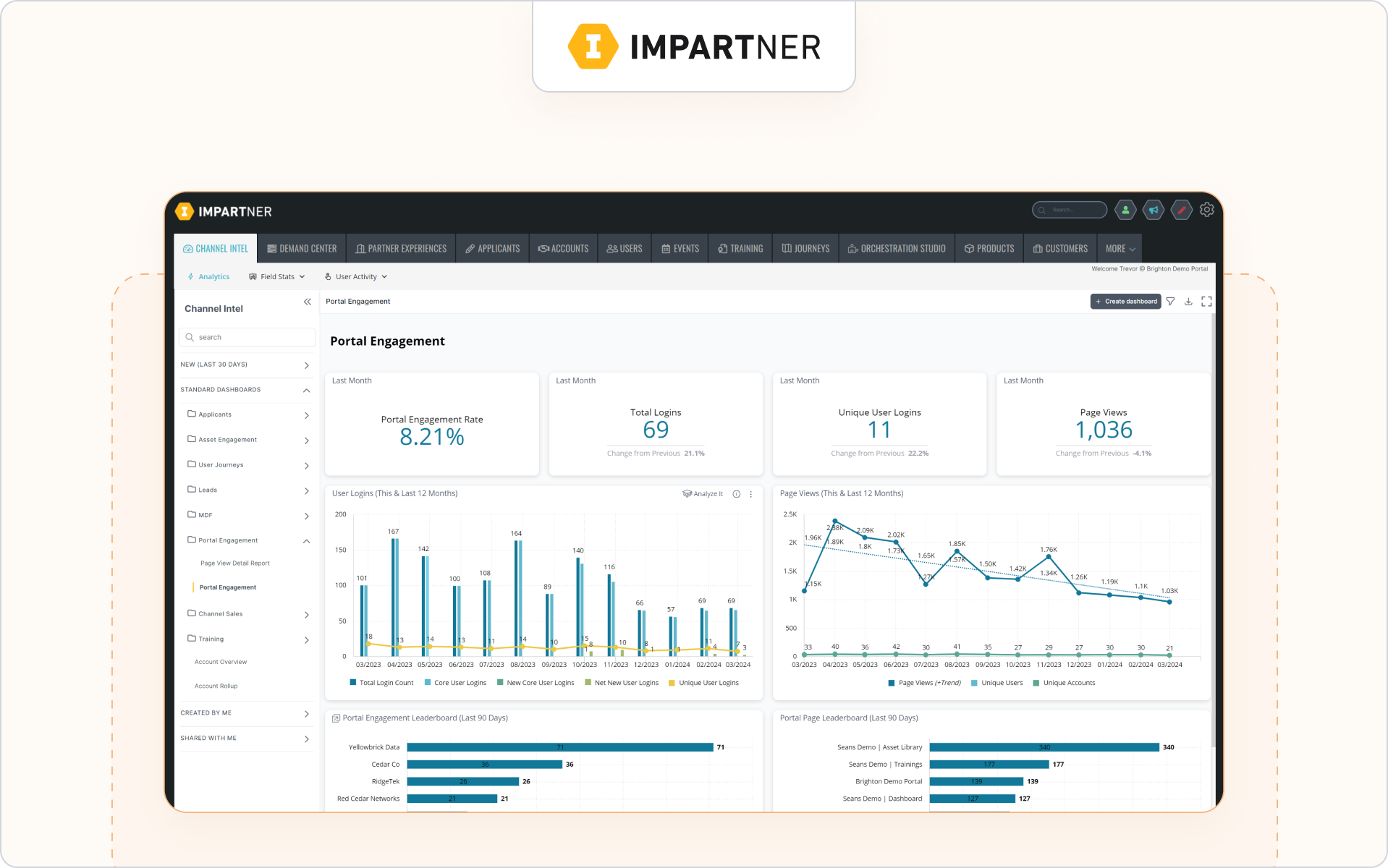
Before choosing a vendor, compare how each partner platform handles real-world complexity across the entire partner lifecycle, not just what the partner portal looks like in a demo.
Why security and scalability now define PRM success
A PRM used to be mostly a partner portal. Today, it exposes deal registration, lead distribution, certifications, content, and partner-facing collaboration across your entire partner lifecycle.
That creates more value. It also creates more risk.
More external users now interact with partner data, customer data, and revenue workflows. Your PRM may support multiple partner programs, regions, and channel sales motions at once. That adds real complexity your team has to manage.
What this changes for security
Security is no longer just infrastructure. It’s about role-based visibility, field-level permissions, secure data sharing, and protecting sensitive data across partner relationships.
What this changes for scalability
Scalability is not user count. It’s whether your system can support multiple partner ecosystems, automated workflows, and structured deal and lead registration without creating manual work for internal teams.
Many platforms look strong in a demo but struggle once real partner management begins at scale. That’s why security and scalability directly shape partner trust, adoption, and revenue operations.
Next, let’s look at what security actually means when evaluating a PRM platform.
How to evaluate PRM security (beyond certifications)
Security certifications matter. They confirm a vendor follows strong security protocols and supports regulatory compliance.
But real PRM security shows up in daily partner management.
It affects how partner data is shared, how access works across partner programs, and how your team handles direct customer interactions inside connected systems. Strong controls help reduce vendor risks, support third-party risk management, and improve risk mitigation across your entire vendor ecosystem.
Here’s what to evaluate first.
.png)
Identity and access controls
Access control is where most security gaps start.
You should be able to control who enters the platform, what they see, and how quickly access can be removed across partner onboarding and channel programs involving multiple partner types.
Look for:
- SSO and SAML support
- MFA for internal teams and partners
- role-based access by partner tier or region
- fast provisioning and removal of users
- secure authentication without manual passwords
These controls reduce cyber risk and strengthen your organization’s security across the vendor lifecycle while supporting consistent third-party risk assessments.
Strong identity controls only work if visibility inside the platform is equally precise.
Granular permissions and data visibility
Most PRM security issues come from oversharing partner data, not infrastructure failures.
A strong permission model lets you control field-level visibility, object-level access, and partner-safe CRM views across different partner journeys. Referral partners rarely need pipeline access, while resellers often do.
You should be able to:
- segment access by partner type, role, or region
- control visibility across deals, contacts, and marketing funds
- protect sensitive data across partner ecosystems
- support structured revenue tracking without exposing unnecessary fields
These controls support vendor risk management and help mitigate risks across the entire supply chain as partners interact with shared workflows.
Platforms built for structured partner management make these controls easier to apply consistently across partner relationships.
Security visibility also depends on whether activity is traceable across the system.
Auditability and governance
If something changes in your partner ecosystem, you should be able to see who did it and when.
Auditability supports risk assessment, compliance risk monitoring, and stronger third-party risk management across the entire partner lifecycle. It also helps teams respond faster to security questionnaires and internal reviews.
Look for:
- activity logs across deals and approvals
- change tracking for shared records
- visibility into deal registration approvals
- traceable partner onboarding updates
- reporting capabilities for compliance reviews
These controls improve risk posture and support ongoing monitoring across your vendor lifecycle, especially when working with high-risk vendors or regulated industries such as a healthcare provider environment.
Content sharing is another place where security gaps often appear.
Content and asset access controls
Modern partner ecosystems depend on shared marketing assets, certifications, and training. That makes content governance part of everyday risk management.
You should be able to control who can access resources, limit visibility by role or region, and track engagement across partner programs. This matters even more when running through channel marketing automation, co-branded email campaigns, or social media syndication.
Platforms with a built-in partner LMS and tools to enable partners with content make it easier to manage content securely without adding manual approval steps.
Strong content controls reduce compliance risks and support consistent security across your entire partner ecosystem.
From here, the focus shifts to whether your PRM can handle growing complexity across partner programs, workflows, and systems.
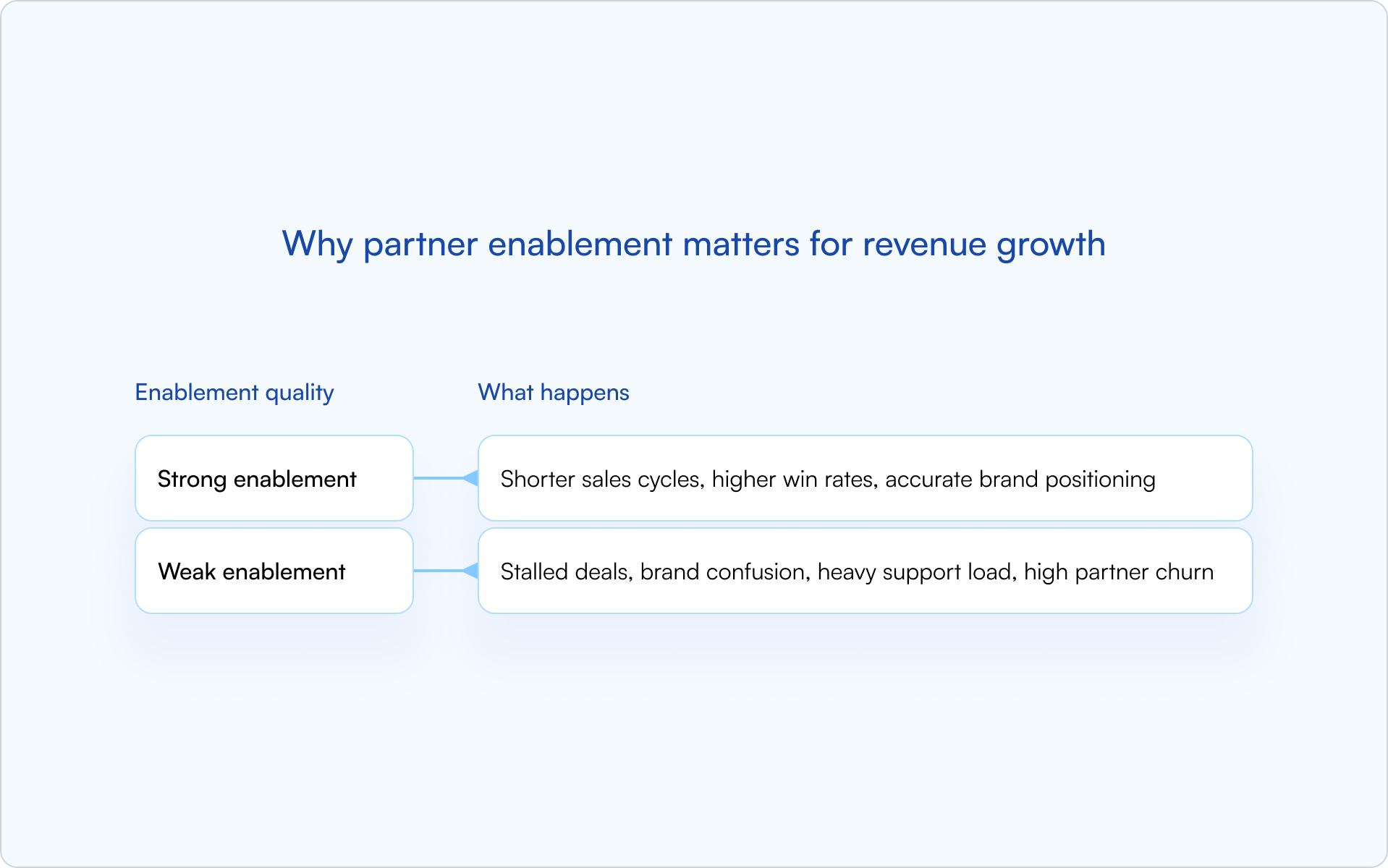
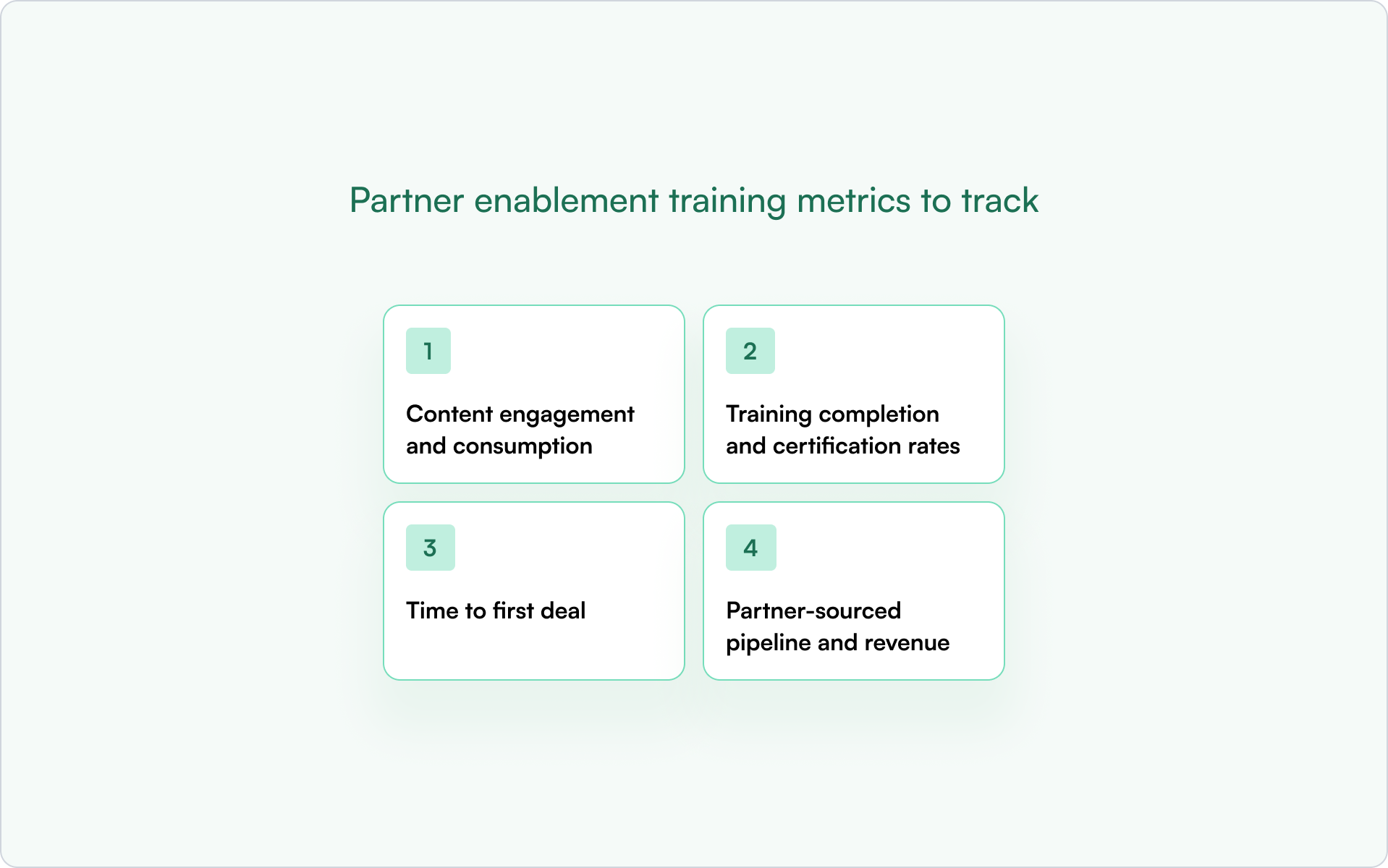
What “scalable” really means in a PRM platform
PRM scalability isn’t about user limits. It’s about supporting more partner programs, partner types, and workflows without adding manual work for your team.
As your ecosystem grows, complexity increases across partner onboarding, approvals, and reporting.
A scalable platform keeps partner engagement steady, supports partner adoption, and maintains revenue visibility across the entire vendor ecosystem.
Here’s what scalability should look like in practice.
Scaling across partner programs and ecosystems
Many PRMs work well with one partner motion. Problems appear when programs expand.
As your ecosystem grows, distributors, resellers, and referral partners often need different pipelines, permissions, and incentive management structures. A scalable platform supports multiple partner journeys inside one unified platform without duplicating setup.
This reduces vendor risks and makes managing risks across the entire supply chain easier across the vendor lifecycle.
Scaling deal registration and engagement workflows
Deal workflows are often the first place scalability breaks.
As your ecosystem grows, distributors, resellers, and referral partners need different pipelines, permissions, and incentive management structures. A scalable platform supports multiple partner journeys in one unified platform without duplication.
Platforms designed for structured partner engagement make it easier to scale collaboration without adding operational risk factors.
Supporting cross-functional internal teams
A scalable PRM should support more than channel managers.
As programs mature, RevOps, marketing, enablement, and leadership rely on the same partner data. Without shared access and real-time visibility, coordination breaks across existing systems.
A dedicated system to manage contacts, track partner onboarding, and support direct customer interactions becomes the central nervous system of your ecosystem.
This improves performance metrics and strengthens the partner experience across programs.
CRM integration and systems scale
CRM integration defines whether a PRM can scale long term.
Your PRM should support deep synchronization with existing systems so partners can collaborate across pipelines, objects, and workflows without creating data handling risks or exposure to data breaches.
Comparing vendors across modern PRM software helps teams maintain data security while scaling workflows across critical phases of partner management.
With that foundation in place, the checklist below helps you evaluate whether a PRM can support both security and complexity as your partner programs grow.
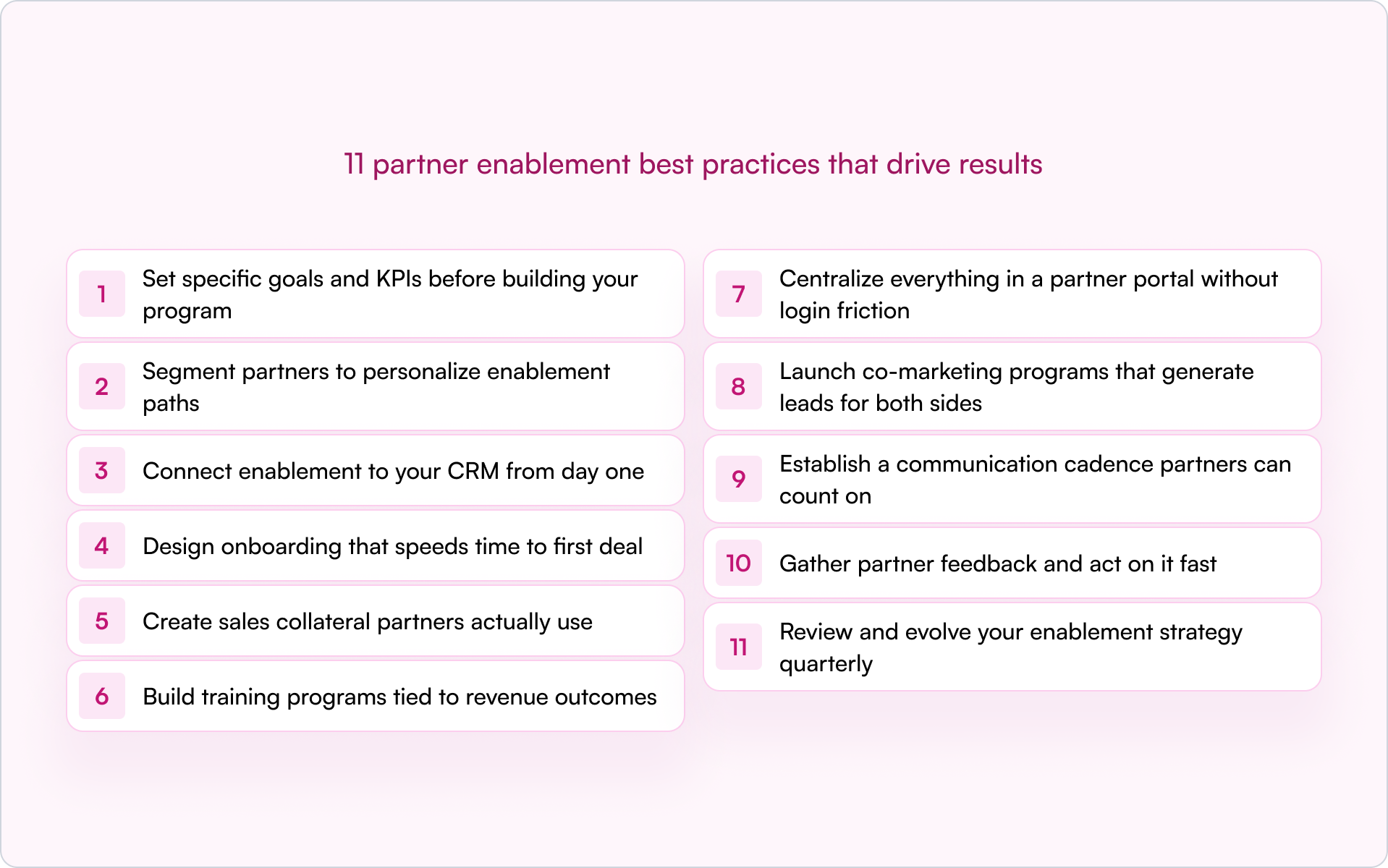
PRM security and scalability checklist for buyers
Use this checklist during vendor selection, demos, and internal risk assessment reviews. It helps your team compare platforms based on real security controls, scalability limits, and how well each system supports long-term partner management.
.png)
1. Identity and access controls
Identity controls determine who can enter your partner portal and what they can see once inside. Weak access rules increase third-party risk quickly, especially as partner programs expand across regions and partner types.
Strong identity controls protect the rest of your partner management environment from avoidable access risks.
2. Permission model and data governance
Permissions decide how safely partner data moves across your ecosystem. Without granular controls, even well-designed partner programs can introduce channel conflict, compliance gaps, and vendor risks.
Flexible permissions help maintain secure collaboration as partner relationships evolve.
3. CRM integration and data visibility controls
CRM integration affects how safely your PRM connects with existing systems and how reliably partner data flows between teams. Weak integrations often create hidden exposure across pipelines and reporting workflows.
Reliable CRM governance supports both scalability and secure long-term partner management.
4. Secure deal registration and approval workflows
Deal workflows directly affect revenue tracking, attribution, and partner trust. If approvals are unclear or inconsistent, they increase financial risk and create friction across partner programs.
Structured deal workflows support predictable collaboration across the entire partner lifecycle.
5. Secure partner collaboration and communication
Partners interact with your systems daily. Those interactions should remain visible, traceable, and controlled across the ongoing process of partner engagement.
Secure collaboration controls protect both partner relationships and internal workflows.
6. Content and enablement access controls
Content sharing is part of everyday partner engagement. Without structure, marketing assets and certifications can become a source of compliance risks across partner programs.
Controlled enablement ensures partners access the right resources without increasing exposure.
7. Scaling across partner types and motions
Most ecosystems include multiple partner motions. A scalable platform should support distributors, resellers, and referral partners without duplicating workflows or creating structural limits.
Support for multiple partner motions keeps programs flexible as ecosystems grow.
8. Admin and reporting at scale
Reporting determines whether teams can actually manage risks across large partner ecosystems. Without structured analytics, partner management quickly becomes manual and fragmented.
Strong reporting capabilities make it easier to compare vendors and choose a platform that scales with your partner programs.
Taken together, these checks help you evaluate how well a PRM supports security, scalability, and day-to-day partner management across your entire vendor ecosystem.
They also make it easier to compare vendors objectively during vendor selection instead of relying on surface-level demos.
If a platform cannot meet these criteria, the limitations usually appear later as channel conflict, reporting gaps, or manual approval work that slows partner engagement and reduces partner adoption.
Before moving forward with a shortlist, it helps to recognize the warning signs teams often overlook during evaluation.
PRM evaluation red flags most buyers miss
Some PRM platforms look strong in a demo but show limits once partner programs expand. These gaps often appear during partner onboarding, reporting, or deal collaboration across multiple partner types.
Watch for these common red flags during vendor selection:
- Permissions are role-based but not field-level, which increases exposure to sensitive data
- CRM sync is one-way, creating gaps across revenue tracking and partner data handling
- Deal registration approvals cannot adapt across regions or partner tiers
- The partner portal supports access, but not partner-safe visibility into shared records
- Reporting lacks comprehensive analytics across partner segments
- Collaboration happens outside the system without audit visibility
- Scaling requires services work instead of configuration inside a unified platform
These limitations increase vendor risks over time and weaken your ability to manage risks across the entire supply chain.
Spotting these issues early helps you ask sharper questions during vendor evaluation meetings.
How to evaluate PRM vendors in demos and internal reviews
You’re probably thinking, 'This might be helpful, but what should I actually ask during a demo?'
This is the stage where vendor selection becomes practical.
Security and scalability claims sound convincing on slides, but what matters is how a platform behaves across your CRM, your partner workflows, and your ongoing process for managing partner programs.
The questions and scorecard below help you evaluate whether a third-party vendor can support automated deal registration, reduce channel conflict, and scale without introducing financial risk later.
16 Questions to ask during a PRM vendor demo
Security and scalability rarely appear in feature lists. They show up in how a platform handles partner visibility, approvals, reporting, and collaboration across real workflows.
Use these questions with every vendor on your shortlist, including Introw.
CRM and data control
- How does partner activity write back to the CRM in real time?
- Can we control which fields partners see at record level?
- How do you prevent duplicate pipelines across partner programs?
- What visibility controls exist beyond a standard partner portal?
Deal registration and conflict prevention
- Does the platform support automated deal registration workflows?
- How are approvals adapted by region, role, or partner tier?
- How does the system detect or reduce channel conflict?
- Can we track deal ownership changes across lifecycle stages?
Security and regulatory requirements
- How does the platform support GDPR and regional regulatory requirements?
- What permissions exist for restricting access to sensitive records?
- How are external partner actions logged for audit visibility?
- Can access be revoked instantly across partner environments?
Reporting and scalability
- What comprehensive analytics exist across partner segments?
- Can reporting track performance across multiple partner tiers?
- How does the system scale across regions and partner types?
- What workflows require services support instead of configuration?
Strong vendors demonstrate these answers directly inside the product instead of describing them in theory.
These responses also make internal comparisons much easier once evaluation moves beyond the demo stage.
A simple internal scorecard for comparing PRM platforms
After vendor demos, most teams rely on notes and impressions. A structured scorecard turns those observations into a consistent vendor selection process.
Score each area from 1 to 5:
- 1 = missing or high risk
- 3 = partially supported with limitations
- 5 = strong native capability
.png)
Platforms that score consistently high across these areas are more likely to support partner programs as they expand across regions, partner types, and revenue motions.
Using a structured scorecard also helps align partnerships, RevOps, and leadership teams around a shared evaluation framework instead of feature-by-feature comparisons alone.
With that foundation in place, it becomes easier to see how a CRM-native platform like Introw approaches security, visibility, and scalable partner collaboration differently from traditional partner portal systems.
How Introw supports security and scalability in PRM
Security and scalability become much clearer when you look at how a platform supports real partner workflows, not just permission settings.
Introw focuses on structured collaboration inside Salesforce and HubSpot while supporting controlled external partner experiences through a partner portal.
This helps SaaS teams scale partner programs without losing visibility across deals, approvals, and enablement activity.
.png)
CRM-native visibility without duplicate partner data
Introw connects directly to Salesforce and HubSpot so partner collaboration stays inside your existing revenue workflows.
Teams can:
- control partner-safe record visibility
- track partner engagement alongside pipeline activity
- maintain audit-friendly interaction history
- avoid syncing partner data across separate systems
This makes it easier to expand partner programs without creating parallel infrastructure.
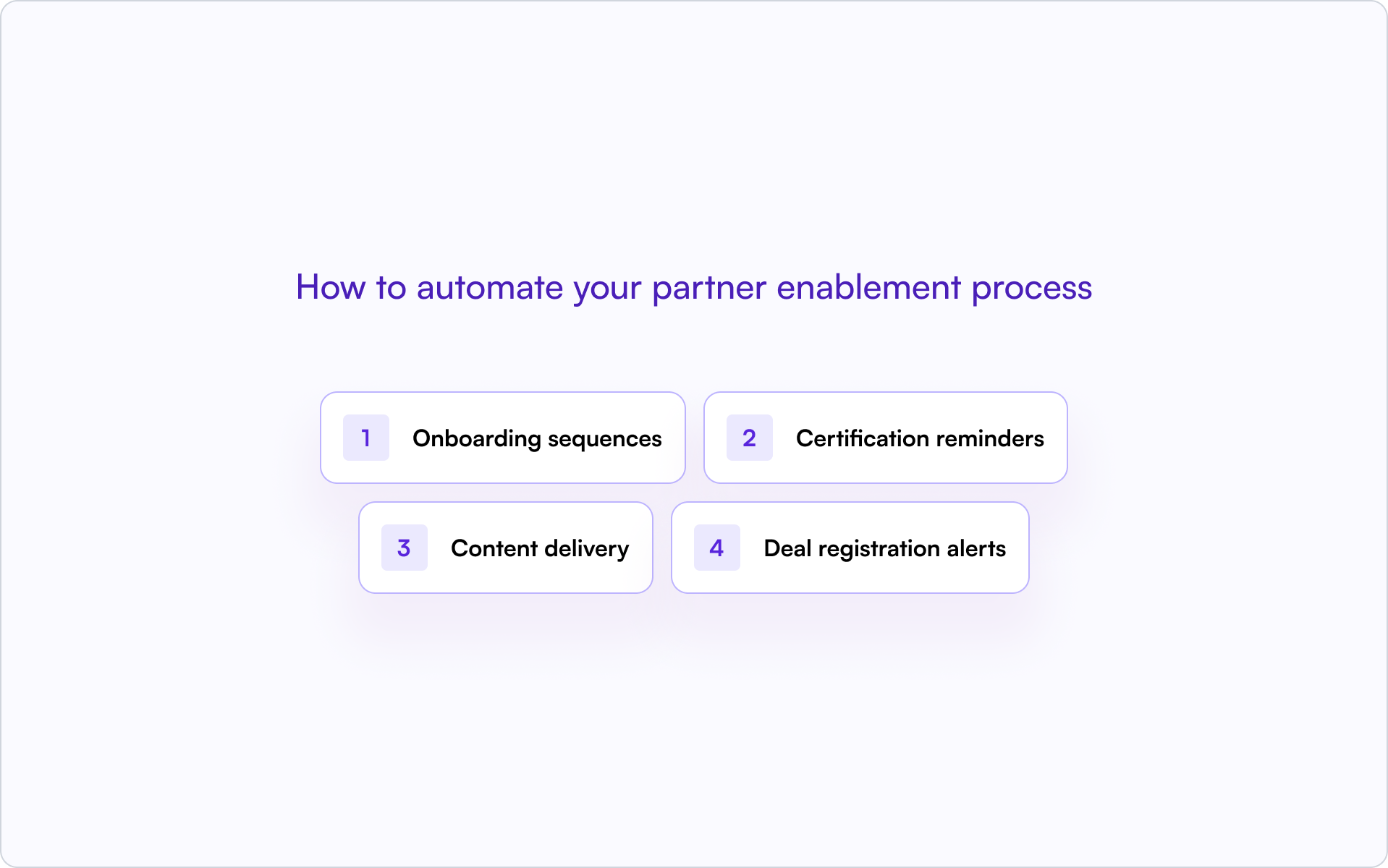
Deal registration and governance across partner tiers
As ecosystems grow, manual approvals increase channel conflict and operational risk.
Introw supports automated deal registration and lead routing workflows that adapt across regions, lifecycle stages, and partner roles. This keeps ownership clearer while maintaining structured governance across partner-submitted opportunities.
Enablement, certifications, and partner content in one environment
Partner readiness depends on timely access to training and sales resources.
Introw includes partner LMS capabilities, certification paths, and partner-facing asset hubs within the same environment. Access can be segmented by role, region, or partner tier so enablement stays aligned with how partners support active opportunities.
This reduces the need for separate training systems or disconnected content portals.
Built to support multiple partner motions as programs grow
Most SaaS ecosystems combine referrals, co-selling, and reseller collaboration.
Introw supports these partner motions inside one shared system while keeping visibility structured across teams and lifecycle stages. Programs can launch quickly using existing CRM data and expand over time without over-engineering early setup.
Integrations also play a role here. For example, teams using the Claude integration can extend partner workflows with AI-assisted coordination and content support without moving collaboration outside their existing environment.
That makes it easier to introduce structure early and scale partner engagement as ecosystems mature.
Over to you
If you're evaluating tools in this category, here are some useful next steps:
- review your current partner workflows and note where visibility or approvals break down
- shortlist the vendors that best match your CRM, partner motions, and governance needs
- bring your checklist into the demo so you can test real workflows, not just UI
If you want to see how Introw fits with your business and teams inside a CRM-native partner environment, request a demo today.
What should I look for in a secure PRM platform
Look for role- and field-level visibility controls, audit logs, GDPR support, and partner-safe access to CRM data without duplicating records in a separate partner portal.
How do I evaluate PRM scalability?
Check whether the platform supports multiple partner tiers, automated deal registration, regional workflows, and reporting across partner segments without requiring services work to expand.
Do I need field-level permissions in a PRM?
Yes. Field-level permissions help protect sensitive pipeline data while still allowing partners to collaborate on shared opportunities.
What makes a PRM scalable for SaaS partner programs?
Scalable PRM platforms support referrals, co-selling, and reseller motions in one system while maintaining structured approvals, visibility controls, and consistent reporting.
How important is CRM integration in PRM evaluation?
CRM integration is critical. It ensures partner activity stays connected to pipeline data, reduces channel conflict, and supports accurate performance tracking across partner programs.


.svg)































.png)



.png)
.png)
.png)
.png)
.png)
.png)